What is ZTZT?
Definition and core principle
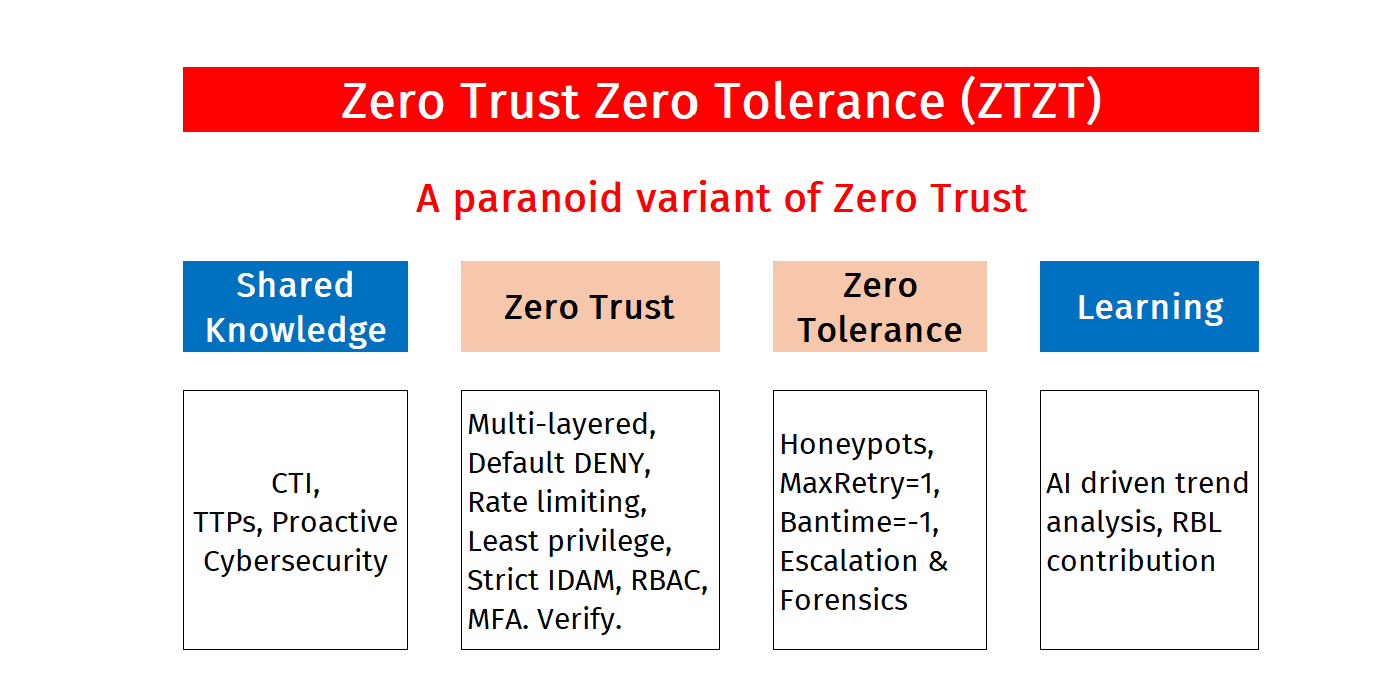
ZTZT (Zero Trust Zero Tolerance) is paranoid variant of Zero Trust, created by Santosh Pandit in 2024 and first implemented at ztzt.dev. It takes no chances of False Negatives.
How is it implemented?
Knowledge Graph
Intelligence-driven defence strategy
- Cyber Threat Intelligence (CTI): We produce our own Threat Intelligence every year. Here are Part 1 and Part 2 of the 2026 forecast. In addition, we generate our own CTI each month and combine it with external CTI. The Threat Intelligence is reviewed and backtested for accuracy each month. (Link to January 2026 review). This helps us stay abreast of the latest cyber threats.
- Tactics, Techniques and Procedures (TTPs): We regularly review the TTPs used by powerful and innovative Threat Actors.
- Proactive Cybersecurity: Our decisions on geoblocking, CIDR blocking and honeypots are driven by CTI, TTPs and log monitoring.
Zero Trust
Core Zero Trust principles
- Multi layer defence: Defense in depth across all system layers
- Default DENY: Firewall and sensitive information access blocked by default
- Rate limiting: Applied to login, user activity, and API calls
- Least privilege: No root access, minimal permissions only
- Strict IDAM: Identity and Access Management enforcement
- RBAC: Role-Based Access Control (e.g. backup operations)
- MFA: Multi-Factor Authentication with strong passphrase protection
Zero Tolerance
Aggressive automated response
- Honeypots (undetectable): Silent traps for threat detection
- Maxretry=1 (automated): Single attempt policy, no second chances
- Bantime=-1 (automated): Permanent bans, no expiration
- Serious threats are manually investigated: Human review for advanced threats
Learning Loop
Continuous improvement through AI
- AI driven trend analysis: Machine learning identifies attack patterns
- Information exchange with RBL: Collaborative threat intelligence sharing
Caution
You are welcome to hack us. But be aware that your IP may be banned. We suggest you contact us so that we can whitelist your IP address.